SQLi Vulnerability and Pentesting Steps
In this lab, you will learn how to analyze the SQLi vulnerability discovered in the SQLi Lab. You will learn what is the vulnerability, how it works, and how to control this vulnerability. You will also learn the steps a pen tester might take when testing for an SQLi.
outcomes:
In this lab, you will learn to:
- Understand the steps of the pen testing process.
- Perform some of the steps of the pen testing process.
Before you start this lab, review these videos.
Determining the Number of Rows
Overview
In this lab we will analyze the vulnerability discovered in SQLi lab, and demonstrate the steps a pentester might take when testing a website for an SQLi vulnerability. The demonstration outlined in this lab will only take you to a certain point, and it will be up to you to proceed from there. Your pentesting assignment will be outlined at the conclusion of this lab.
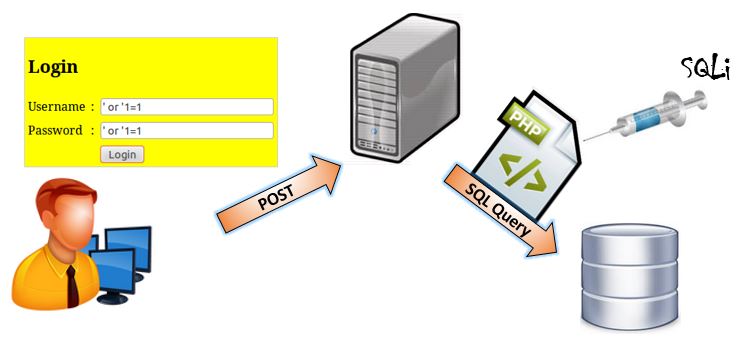
SQLi Vulnerability and Pentesting Steps