Signature Detection and Remote Shells
In the lab, you will learn how to launch a remote shell, create a SNORT rule to prevent remote shells, and verify the SNORT rule prevents the launching of a remote shell.
OUTCOMES:
In this lab, you will learn to:
- Launch an nc listener
- Create a BASH shell to connect to nc listener
- Create a rule in SNORT
- Test a SNORT rule
videos:
Before you start this lab, review these videos.
Setting Up the Virtual Environment
Client-Side Commands for Remote Shells
Overview
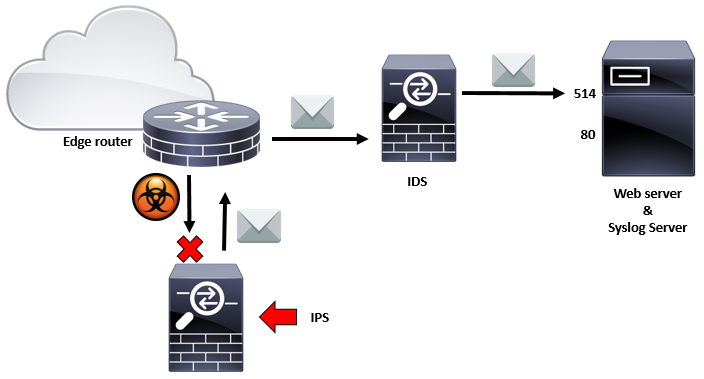
Signature detection is useful in stopping known threats when used in coordination with an Intrusion Prevention System (IPS). This lab will demonstrate how to prevent remote shells using signatures created in SNORT running in inline mode.
Signature Detection and Remote Shells
Key terms and descriptions
remote shell
A remote shell is a command-line interpreter that executes commands.
wireshark
Wireshark is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications protocol development, and education.
BASH Shell
Bash is a Unix shell and command language written by Brian Fox for the GNU Project as a free software replacement for the Bourne shell.
SNORT
Snort is a free open source network intrusion detection system (IDS) and intrusion prevention system (IPS) created in 1998 by Martin Roesch.