Session Stealing (Remote Reflected XSS)
In this lab, you will learn how to launch a remote reflected XSS attack using phishing and you wlll also learn how to steal session IDs from a cookie. You will learn to use Uniform Resource Locator (URL) to encode characters using a web page in Ice Weasel.
outcomes:
In this lab, you will learn to:
- Use phishing to launch a remote reflected XSS attack.
- Use the Cookies Manager to steal a session ID in a browser.
videos:
Before you start this lab, review these videos.
Overview
Session IDs are long randomized values used to uniquely identify a user with an application. If a session ID happens to get stolen, the result could lead to unauthorized access. In this lab, we will demonstrate session stealing, where Bob the hacker is able to obtain Alice the administrator’s session ID through a remote reflected XSS attack. He will then use a Firefox plugin to steal Alice’s session.
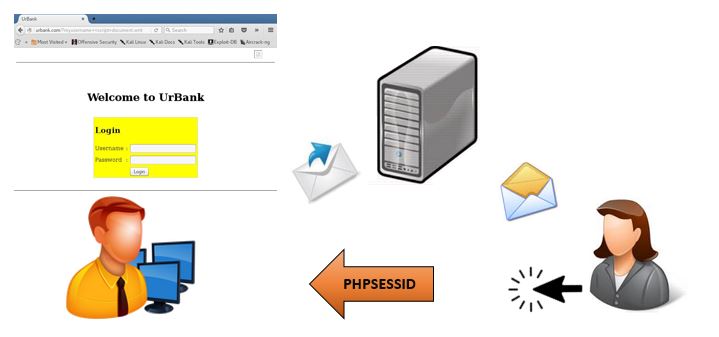
Session Stealing
Key terms and descriptions
Insertion only occurs within the client-side file.
Information is not reflected back to the local user. Instead, the information is sent to a specific location.