Pentesting the Forum
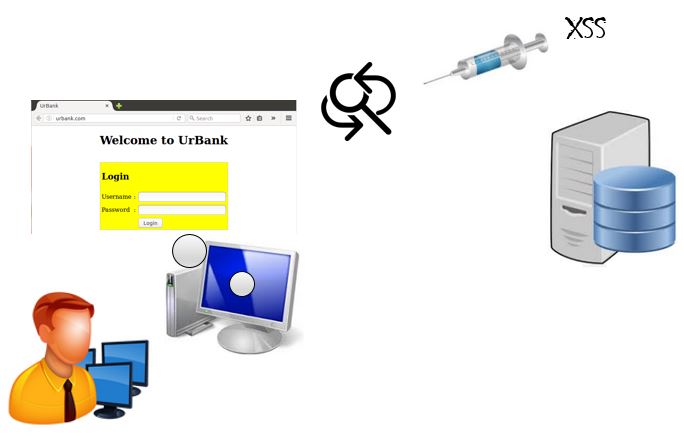
In this lab, you will learn how to control and bypass a stored Cross-Site Scripting (XSS) vulnerability. You will also learn how the addslashes function can be used to disallow some SCRIPT elements from executing. However, it is important to note that it will not disallow all SCRIPT elements.
outcomes:
In this lab, you will learn to:
- Implement a security control for stored XSS vulnerability.
- Bypass the implemented security control.
videos:
Before you start this lab, review these videos.
Overview
In this lab, we demonstrate why the input being supplied to the forum must be secured. Then we will implement a security control that will mitigate the attack and ask you to bypass it in a pentesting assignment. We will use the Ubuntu client to implement the security control and run the setup script. All pentesting will be performed from Kali.
Pentesting the Forum
Key terms and descriptions
World Wide Web
The World Wide Web (www) is a client–server system that allows documents and web resources be available over the Internet.
Uniform Resource Locator
Each document/web resource is represented as a Uniform Resource Locator (URL).
Hypertext Transfer Protocol
Hypertext Transfer Protocol (HTTP) is an application layer protocol that allows web browsers to communicate with web servers.
Hypertext Markup Language
The Hypertext Markup Language (HTML) is the standard format of a web page.
Hypertext Preprocessor
Hypertext Preprocessor (PHP) is a server-side scripting language used to create web applications.
Cross-Site Scripting
Cross-Site Scripting (XSS) is a type of injection attack that involves exploitations through code.