Overview
Compliance Use Case: Comply with Acceptable Use Policy
Description: The purpose of any Acceptable Use policy is not necessarily to impose restrictions, but to define the appropriate use of computer equipment. These policies help protect employees from risks associated to attacks, compromise of network systems and services, or legal issues.
Security Type: Compliance, Network Security
Threat Actors: Insiders
Threat Actors' Goals: N/A
Your Task: Using LogRhythm's Web Console Dashboards and Analyzer Grid, locate any logs that may be an indication of inappropriate activity.
- Data to look out for might include some network traffic by a certain user violating a Use Policy while on the job.
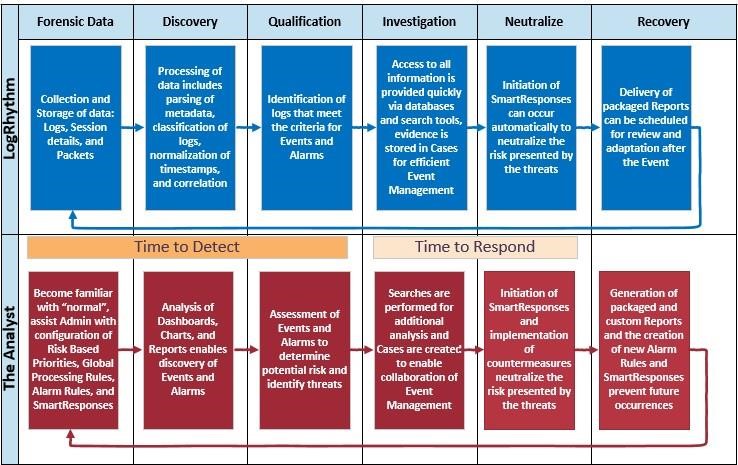
- Work the incident through the Threat Lifecycle Management process and document your findings as you go.
There is a generic technique for using the LogRhythm Web Console for threat hunting. You need to familiarize yourself with the log data in your environment by looking at the Web Console, dashboards, alarms, reports, and running searches. This helps you discover things that should not be occurring in your environment abnormal and usually rare. Some of the best tools in the Web Console for discovering threats are:
- The time range filter
- Alarms
- Top Classification
- Top Common Events
- Top Log Source Type widgets
Once you have discovered a threat, you need to decide whether you actually need to do something about it. This is known as qualifying the threat. Then you can investigate the threat using pivots, drilldowns, searches, reports, and cases. Next we neutralize the threat; we stop the problem from getting worse. Lastly, we recover. We determine how we will prevent this and similar types of things from happening again.