Overview
Analyst Goal: Begin exploring real-world security use cases within the LogRhythm SIEM
Description: In this lab, you will run some Python scripts which will inject log data into your lab environment. Your job is to work through the exercises below to find the threat situations you introduced into the system. You should follow the Threat Lifecycle Management framework to detect and neutralize the threat.
Task: Run the Python scripts at the designated times and hunt down the threats.
Taking Action Using LogRhythm
The objective of this chapter is to practice detection and response to scripted scenarios in LogRhythm.
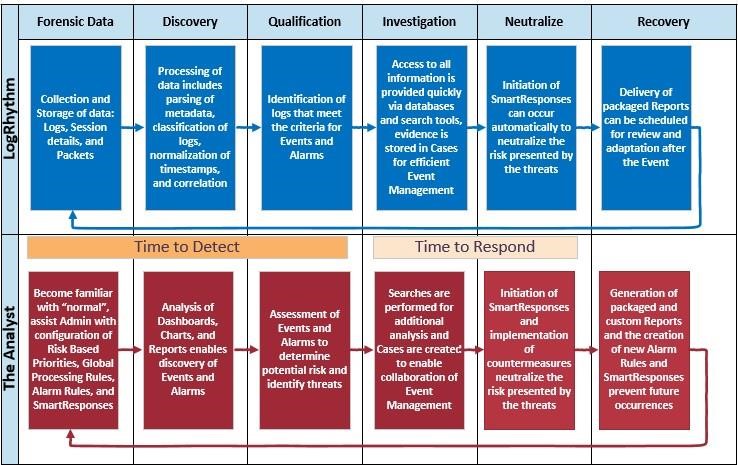
Organizations today are increasingly concerned about security and operational type events, and compliance requirements. LogRhythm's unified security intelligence and analytics platform enables analysts to detect, prioritize, and neutralize cyber threats that have penetrated the perimeter or originate from within.
This chapter employs a hands-on approach allowing you to practice taking action using LogRhythm to detect and respond to various security, operations, and compliance type events. Using this approach consistently will ensure the timely detection and mitigation of threats in your environment.
There is a generic technique for using the LogRhythm Web Console for threat hunting. You need to familiarize yourself with the log data in your environment by looking at the Web Console, dashboards, alarms, reports, and running searches. This helps you discover things that should not be occurring in your environment abnormal and usually rare. Some of the best tools in the Web Console for discovering threats are:
- The time range filter
- Alarms
- Top Classification
- Top Common Events
- Top Log Source Type widgets
Once you have discovered a threat, you need to decide whether you actually need to do something about it. This is known as qualifying the threat. Then you can investigate the threat using pivots, drilldowns, searches, reports, and cases. Next we neutralize the threat; we stop the problem from getting worse. Lastly, we recover. We determine how we will prevent this and similar types of things from happening again.