IDS, SYSLOG, and NTP
IDSs and syslogs are integral pieces of any network security setup. IDSs detect potential threats on a network and syslogs send & store events depending on the classification. Both of them provide system/network visibility and be crucial in finding past, present, and potential future threats.
outcomes:
In this lab, you will learn to:
- Install SNORT
- Configure the Syslog server
- Install an NTP server
videos:
Before you start this lab, review these videos.
Setting Up the Virtual Environment
Overview
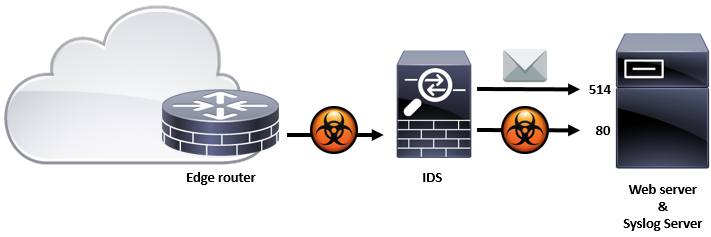
An Intrusion Detection Systems (IDS) is a software application that can be used to detect threats within a network. Syslog is a software application that can send and store events based on classification. Both of them provide system/network visibility and be crucial in finding past, present, and potentially future threats. In this lab, we are going to install an IDS on the host (IDS-DMZ.urbank.com) using SNORT software and configuring it to send messages to a Syslog server. In this lab we will also configure the host (urbank.com) to take the Syslog server role using the RSYSLOG software utility. Lastly, we install the and configure the ntp package on both IDS-DMZ.urbank.com and urbank.com to ensure sychronized logging.
IDS and RSYSLOG