HTMLi Vulnerability and Mitigation
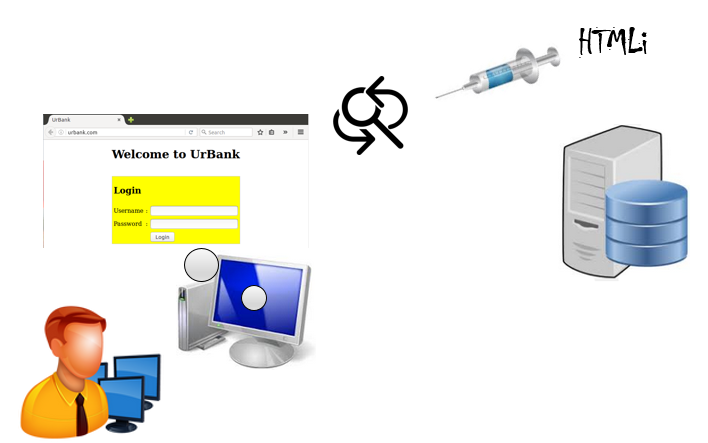
HTMLi injection is a type of cross-site scripting attack that allows for malicious code to be injected into a site. In this lab, you will analyze the HTML injection, how the HTMLi works, and also learn to control for the HTMLi injection in PHP.
outcomes
In this lab, you will learn to:
- Analyze the HTMLi.
- Implementing a Security Control for HTMLi.
Videos:
Before you start this lab, review these videos.
https://www.youtube.com/watch?v=2R9RclByAis - Describing the Action Script
https://www.youtube.com/watch?v=PZwch18dulI - Analysis of the Vulnerability
https://www.youtube.com/watch?v=-x0GsSW6nrQ - Implementing a Security Control
https://www.youtube.com/watch?v=gxjcFzuTeog - Verifying the Control Works
Overview
PHP has many filters that can be used to mitigate attacks. However, if the filters are wrongly used or have been deprecated, they can be bypassed. In this lab, we begin by provisioning the virtual environment and give a brief description of the action script used to collect and store usernames and passwords stolen from the HTML form in HTML Injections lab. Then we will provide a brief description of the vulnerability and implement a control in an attempt to prevent the complete INPUT element from being injected and rendered. After demonstrating how the control works, you will be tasked with circumventing the control by allowing the input field to be displayed on the webpage. Implementation of the control and running the script will be performed from the Ubuntu client, and all pentesting will be performed from Kali.
HTMLi Vulnerability and Mitigation