Abusing a Stateless Firewall
In this lab, you will perform a denial-of-service attack using Python’s Scapy module and hping3 command against the stateless firewall protecting the web server.
outcomes:
In this lab, you will learn to:
- Attack a firewall with a DoS with Scapy.
- Attack a firewall with a DoS with hping3.
videos:
Setting Up the Virtual Environment
Overview
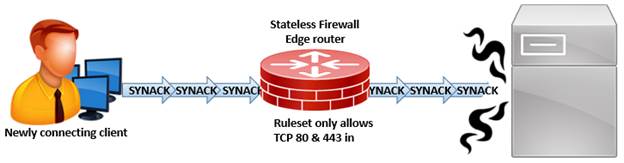
A stateless firewall can be used to minimize the risk associated with certain attacks. However, a stateless firewall does not retain the state for a given connection. This lab will demonstrate how a stateless firewall will allow a new connecting client to send a TCP SYN ACK packet as the first means of communication with the server. Then, we will use Hping3 to demonstrate a TCP SYN ACK DoS attack. The pentesting assignment for this LAB will be to craft a TCP SYN ACK DoS attack using Scapy.
Abusing a Stateless Firewall